Mobile Security: Protecting Your Smartphone
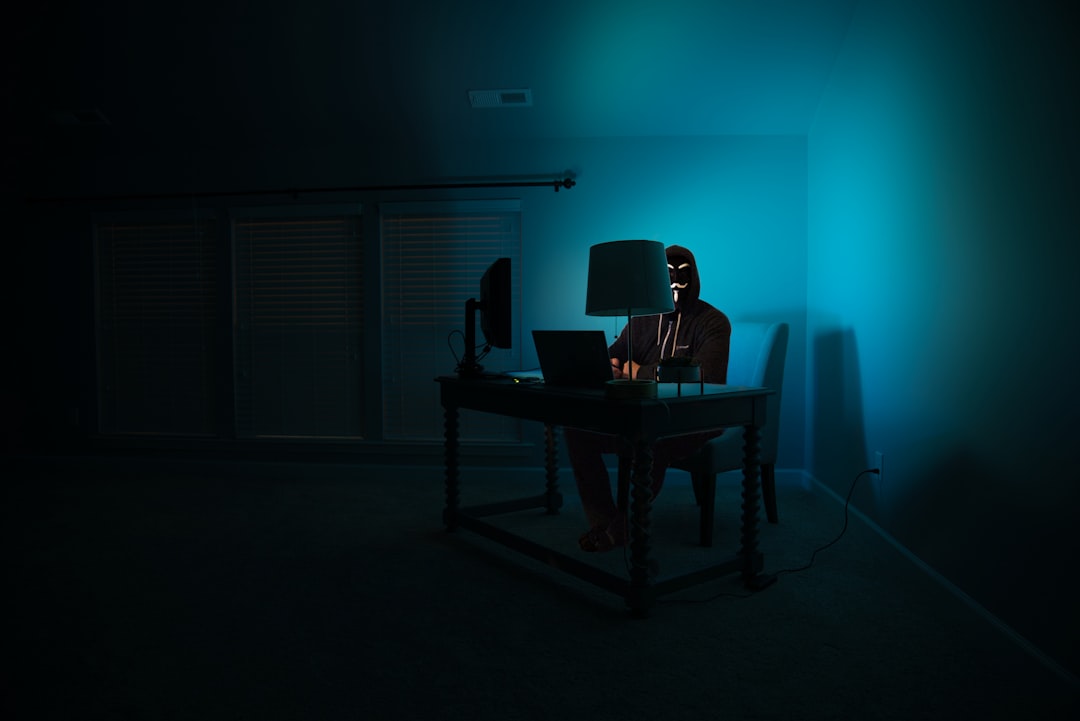
Mobile Security: Protecting Your Smartphone Introduction Your smartphone contains more personal information than your wallet, diary, and filing cabinet combined. From banking apps and email accounts to photos and location data, your mobile device is a treasure trove for cybercriminals. Mobile security isn’t just about protecting your phone—it’s about safeguarding your entire digital identity. Understanding … Read more