Public WiFi Security Risks and How to Stay Safe
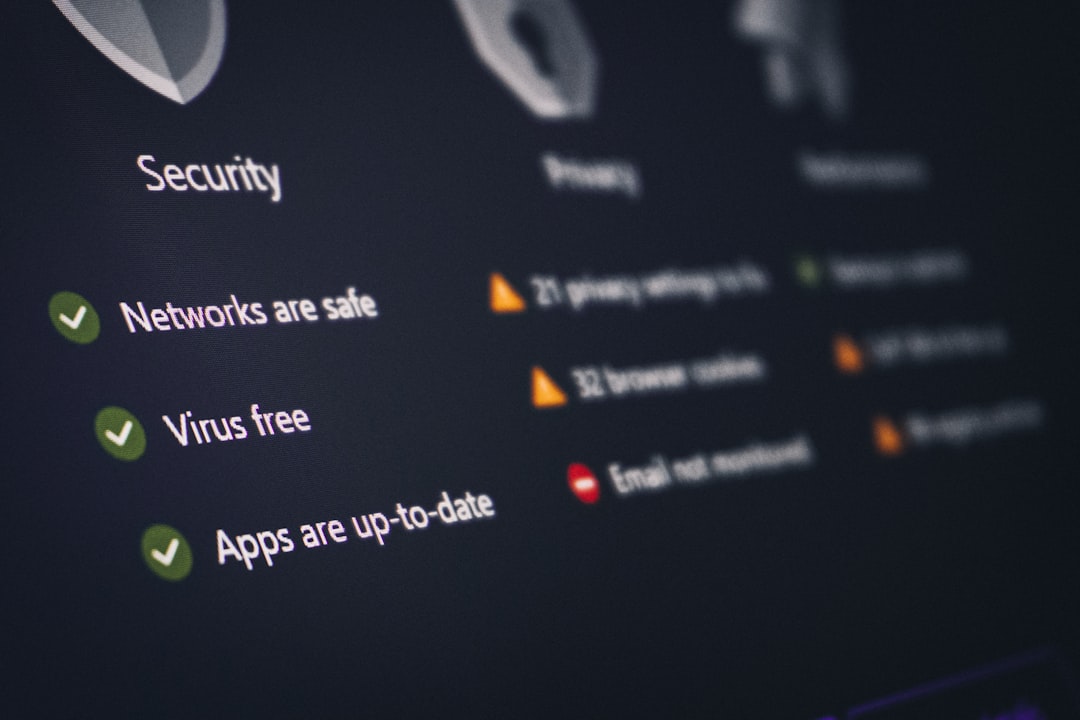
Public WiFi Security Risks and How to Stay Safe Quick Take Public wifi security threats are real, but they’re also completely manageable with the right precautions. The single most important thing you can do: use a VPN (Virtual Private Network) whenever you connect to public wifi. A VPN encrypts all your internet traffic, making it … Read more